Latest News
Federal appeals court hears arguments on nation’s first ban on gender-affirming care for minors
By Andrew DeMillo and Jim Salter, AP
LGBTQ+ events in NYC
Tomorrow, 4:30 pm
Tomorrow, 5 pm
Tomorrow, 6 pm
April 23, 8 pm
Perspectives
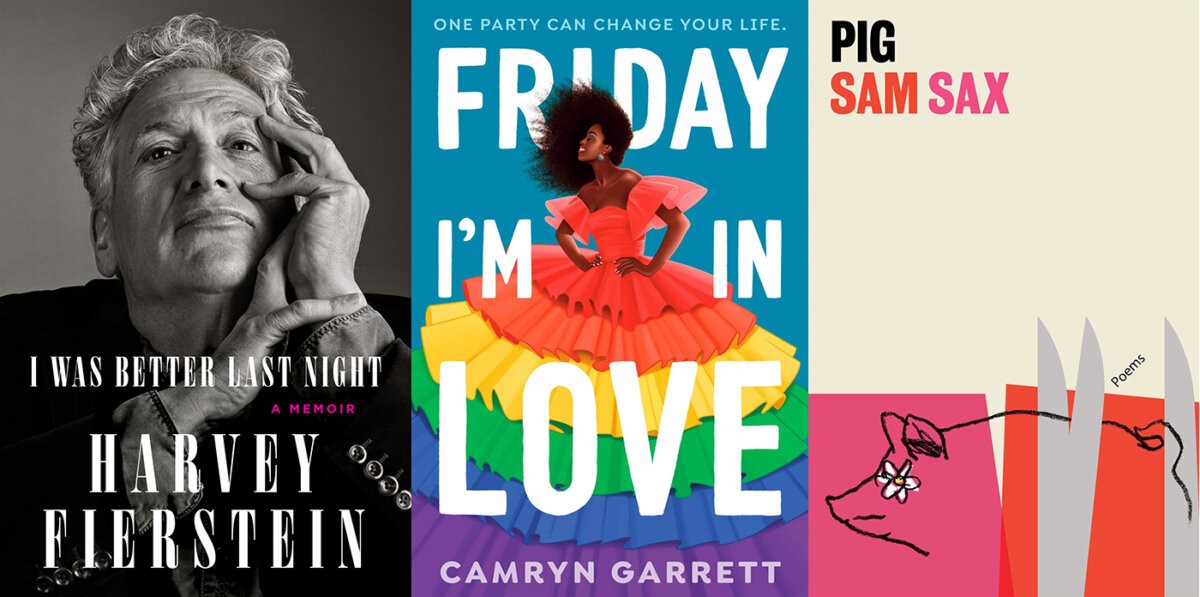
Arts
 Trans-led scuba diving company caters to queer travelers
Trans-led scuba diving company caters to queer travelers Heartbeat Opera spins ‘Eugene Onegin’ and introduces ‘The Extinctionist’
Heartbeat Opera spins ‘Eugene Onegin’ and introduces ‘The Extinctionist’ Q&A with ‘Egoist’ director Daishi Matsunaga
Q&A with ‘Egoist’ director Daishi Matsunaga ‘John Jarboe: The Rose Garden’ was inspired by a local creative’s personal journey
‘John Jarboe: The Rose Garden’ was inspired by a local creative’s personal journey ‘Sperm Donor Wanted’ review: And baby makes five?
‘Sperm Donor Wanted’ review: And baby makes five?
Crime
 No punishment for cops in Kawaski Trawick case, NYPD says
No punishment for cops in Kawaski Trawick case, NYPD says Two men arrested on drug charges in Cecilia Gentili’s death
Two men arrested on drug charges in Cecilia Gentili’s death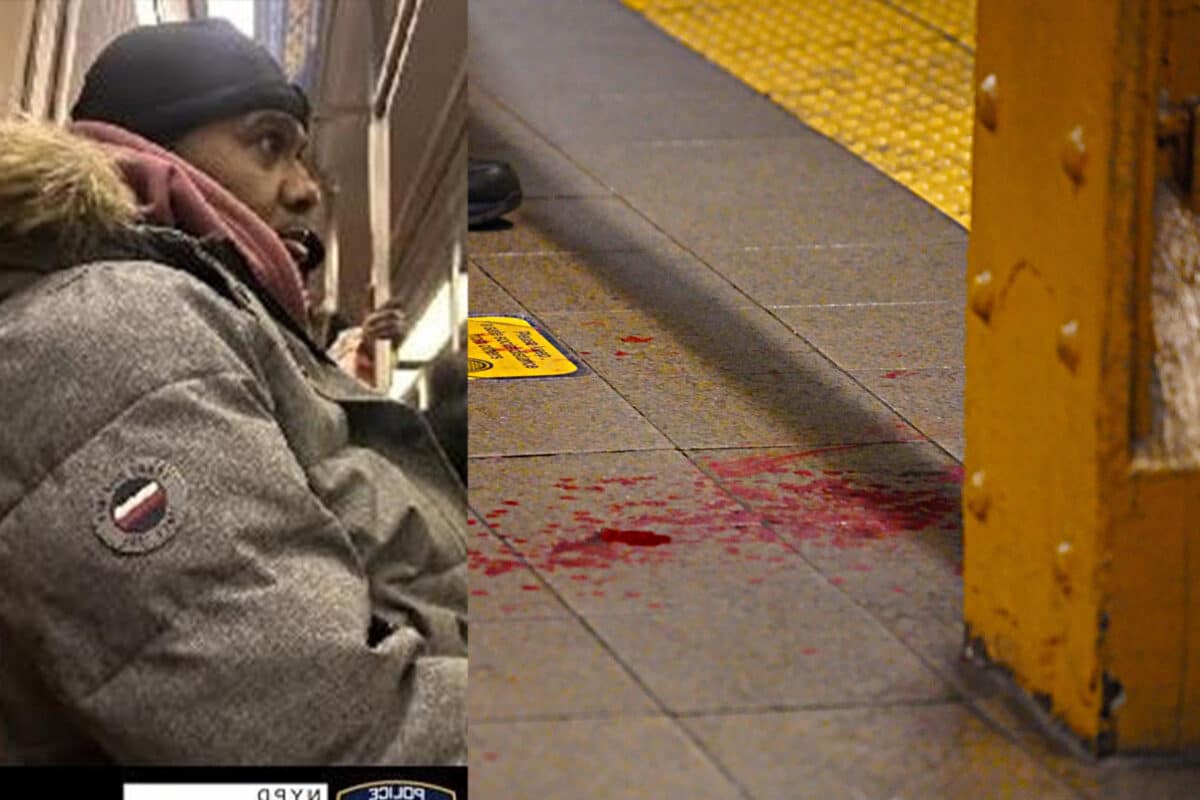 Bigot with box cutter attacks gay man on board A train in Midtown: cops
Bigot with box cutter attacks gay man on board A train in Midtown: cops Man guilty in Black transgender woman’s killing in 1st federal hate crime trial over gender identity
Man guilty in Black transgender woman’s killing in 1st federal hate crime trial over gender identity ‘We must demand justice’: Non-binary teen’s death in Oklahoma sparks national attention
‘We must demand justice’: Non-binary teen’s death in Oklahoma sparks national attention
Politics
 Biden campaign launches ‘Out for Biden-Harris’ to mobilize LGBTQ voters
Biden campaign launches ‘Out for Biden-Harris’ to mobilize LGBTQ voters Hundreds remember David Mixner’s life and legacy in NYC
Hundreds remember David Mixner’s life and legacy in NYC The Trump camp and the White House clash over Biden’s recognition of Transgender Day of Visibility
The Trump camp and the White House clash over Biden’s recognition of Transgender Day of Visibility Spending bill excludes most anti-LGBTQ riders, but bans Rainbow Flags at State Department
Spending bill excludes most anti-LGBTQ riders, but bans Rainbow Flags at State Department Out electeds rip Manhattan community education council over anti-trans sports resolution
Out electeds rip Manhattan community education council over anti-trans sports resolution